A fast-moving iPhone spyware causes Apple users to update immediately.
A new iPhone hacking chain named DarkSword hit the security world this week and quickly turned into one of Apple’s biggest mobile security stories of 2026. Researchers said the tool was already active in the wild, and reports linked it to campaigns targeting users through compromised websites. The scale caught attention fast because the exposed software range covered a very large share of iPhones still in use.
The reports painted a simple but ugly picture. A user could visit a malicious page and lose access to deeply personal data in seconds. Researchers said the exploit chain targeted iOS 18 builds, especially versions in the 18.4 through 18.6.2 range, while Google’s threat team said DarkSword support extended through iOS 18.7. Apple responded by telling users to update and stressed that patched devices were already protected.
That matters because this was not a small lab demo or a hacker forum fairy tale. According to Reuters reporting and technical findings from Google Threat Intelligence Group, the exploit chain was used in real campaigns and had been in use since at least November 2025. Researchers linked activity to attacks in Saudi Arabia, Turkey, Malaysia, and Ukraine. iVerify said some of the infrastructure overlapped with the earlier Coruna activity disclosed this month.
What’s Happening & Why This Matters
DarkSword Turns a Website Visit Into a Full Compromise
DarkSword is a full-chain iOS exploit. That means it does not rely on a single bug. Google said the chain used six vulnerabilities to compromise devices and then deploy follow-on malware fully. The company said it identified three malware families after compromise: GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER. That gives this story extra teeth. One weak link is bad enough. Six working together is a burglar with a key ring and a floor plan.

Researchers described DarkSword as fast, quiet, and built for data theft. Reuters reported that the spyware was capable of stealing information from potentially hundreds of millions of iPhones. Coverage from Euronews and other outlets said the stolen data could include messages, emails, location history, and more. iVerify described the affected base as up to 270 million devices running exposed iOS 18 versions.
The attack method also matters. This was described as a watering hole operation. Attackers compromised websites and then redirected victims to malicious payloads. iVerify said one redirecting site even used a Ukrainian government domain, which raised the stakes and showed how normal browsing could become risky in the wrong campaign. That is the part that average users often miss. You do not need to click a giant neon sign that says “FREE CRYPTO.” A familiar site can be enough if an attacker has already poisoned the well.
A More Serious Threat Than a One-Off Spyware
Google’s 18 March post said DarkSword had been used by multiple commercial surveillance vendors and suspected state-sponsored actors. That detail takes this story beyond the usual one-group, one-region breach headline. It suggests an exploit chain that spread across more than one operator, more than one campaign, and more than one playbook.

Reuters added more context. Its report said researchers linked DarkSword activity to dozens of Ukrainian websites in recent weeks and noted concern that the same tool or related infrastructure appeared in campaigns tied to Russia and other actors. That makes DarkSword appear less like a rare precision missile and more like a weapon moving around an active marketplace. Once those tools circulate, risk expands. The attack surface does not stay reserved for spies in trench coats. It drifts toward criminals, copycats, and operators with fewer rules and lower skill.
This is the second big iPhone exploit story in a short span. Google said DarkSword’s spread mirrored the earlier Coruna iOS exploit kit. Apple’s 11 March security pages for older devices explicitly said some fixes were associated with the Coruna exploit. Put bluntly, Apple users are not looking at one isolated thunderstorm. They are standing under a weather system.
Apple Says: Update!
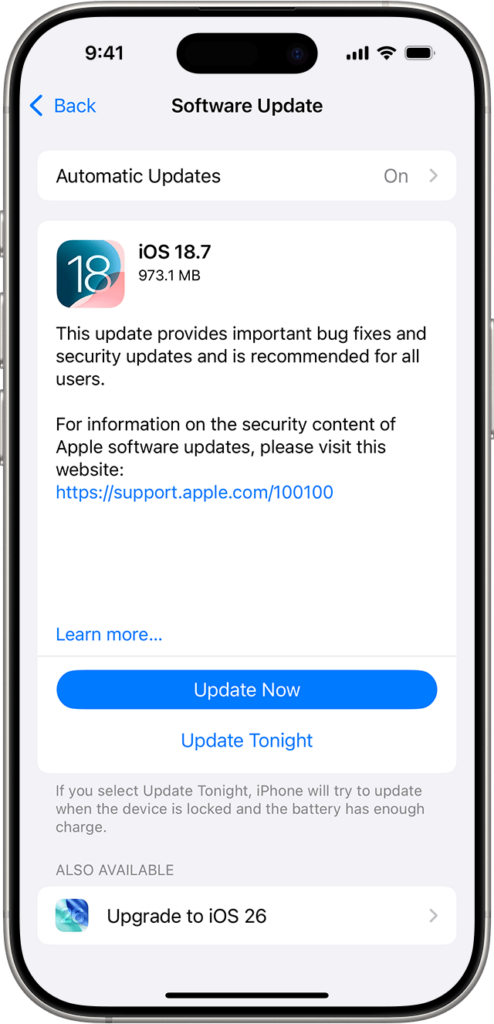
Apple’s public guidance on 19 March was unusually direct. The company said, “Keeping your software up to date is the single most important thing you can do”, and added that devices with updated software were not at risk from the reported attacks. Apple said Lockdown Mode protected users against the specific attacks, even on out-of-date software, though it still urged people to update as soon as possible.
Apple said the latest versions of iOS, from 15 through 26, were already protected. It said it released updates for iOS 15 and iOS 16 on 11 March 2026 to extend protection to older devices that cannot move to the latest iOS. On top of that, Apple noted that Safari Safe Browsing blocks the malicious domains identified in the attacks by default. That is good news, but it is a quiet warning: browser protections help, yet they are not a substitute for patching.
Apple’s own update pages also show how long the exposed iOS 18 branch stayed in circulation. The support page for iOS 18 lists versions from 18.4 through 18.7.6, while several entries state that important security fixes are “recommended for all users.” In other words, the company had already been shipping protection across that branch, but millions of devices still appear to have remained behind. That gap between available patches and installed patches is where attackers throw a party.
Why All User Types Need to Care
The practical risk here is not abstract. Google said DarkSword can deliver payloads after full compromise. Reuters and other coverage described the target data as comprehensive and personal. That puts ordinary users at risk, but it raises the danger for people with higher exposure: journalists, executives, public officials, activists, and anyone who stores sensitive work data or crypto wallet access on an iPhone.

The story chips away at a common myth. Many users still treat the iPhone as if it were a gated castle with a dragon at the bridge and a polite sign that says “No Malware Today, Thanks.” Apple’s security model remains strong, but strong is not magic. When exploit chains reach the web layer, traverse multiple bugs, and land in active campaigns, user hygiene is part of the defense stack. Update discipline matters. Lockdown Mode matters for at-risk users. Safe browsing protections matter. Delay does not. Delay is what turns “there is a patch” into “there was a breach.”
The other lesson is strategic. DarkSword shows how mobile spyware, commercial exploit vendors, and state-linked operations collide in the same room. That is bad for Apple, bad for defenders, and worse for users who assume mobile threats still trail desktop threats by years. They do not. Phones are identity vaults, message archives, location trackers, health logs, and payment devices in one slab of glass. Attackers know it.
TF Summary: What’s Next
DarkSword exposed a painful truth for Apple users: even a premium security reputation does not protect devices that stay behind on updates. Researchers from Google, iVerify
, and others tied this exploit chain to real campaigns, real victims, and a very large pool of exposed iPhones. Apple responded with a clear message: patched devices are protected, older devices received added fixes, Safari blocks known malicious domains, and Lockdown Mode offers extra defense.
MY FORECAST: Apple will continue tightening its rapid-response security delivery, and mobile threat reporting will grow louder in 2026. Expect more attention on background security updates, faster out-of-band fixes, and more public pressure on users and enterprises to keep iPhones current. DarkSword will not be the last named mobile exploit chain this year. It looks more like the opening act than the finale.
— Text-to-Speech (TTS) provided by gspeech | TechFyle